Archive - 70-742: Identity with Windows Server 2016
Sample Questions
Question: 290
Measured Skill: Implement identity federation and access solutions (15–20%)
You have servers that run Windows Server 2016 and devices that run Windows 10 Enterprise. You have a certification authority (CA) that Issued computer certificates to all the servers and devices.
You plan to allow the Windows 10 devices to connect to the network remotely by using VPN device tunnels.
You install the Remote Access server role on a server. From the Routing and Remote Access console, you configure the server for the VPN role.
You need to ensure that the Windows 10 devices can establish the VPN tunnel before users sign in to the devices.
What should you do on the VPN server?| A | Modify the ports properties and add additional SSTP ports. |
| B | Modify the ports properties and add additional IKEv2 ports. |
| C | From Authentication Methods, select Extensible authentication protocol (EAP). |
| D | From Authentication Methods, select Allow machine certificate authentication for IKEv2. |
Correct answer: DExplanation:
Always On VPN gives you the ability to create a dedicated VPN profile for device or machine. Always On VPN connections include two types of tunnels:
Device tunnel connects to specified VPN servers before users log on to the device. Pre-login connectivity scenarios and device management purposes use device tunnel.
User tunnel connects only after a user logs on to the device. User tunnel allows users to access organization resources through VPN servers.
Unlike user tunnel, which only connects after a user logs on to the device or machine, device tunnel allows the VPN to establish connectivity before the user logs on. Both device tunnel and user tunnel operate independently with their VPN profiles, can be connected at the same time, and can use different authentication methods and other VPN configuration settings as appropriate. User tunnel supports SSTP and IKEv2, and device tunnel supports IKEv2 only with no support for SSTP fallback.
User tunnel is supported on domain-joined, nondomain-joined (workgroup), or Azure AD–joined devices to allow for both enterprise and BYOD scenarios. It is available in all Windows editions, and the platform features are available to third parties by way of UWP VPN plug-in support.
Device tunnel can only be configured on domain-joined devices running Windows 10 Enterprise or Education version 1709 or later. There is no support for third-party control of the device tunnel. Device tunnel does not support using the Name Resolution Policy table (NRPT). Device tunnel does not support Force tunnel. You must configure it as Split tunnel.
Device Tunnel Requirements and Features
You must enable machine certificate authentication for VPN connections and define a root certification authority for authenticating incoming VPN connections.
Reference: Configure VPN device tunnels in Windows 10
Question: 291
Measured Skill: Manage and maintain AD DS (15–20%)
You have a server named Server1 that runs Windows Server 2016. Server1 is a Hyper-V host that hosts a virtual machine named VM1.
Server1 has three network adapter cards that are connected to virtual switches named vSwhitch1, vSwitch2, and vSwitch3.
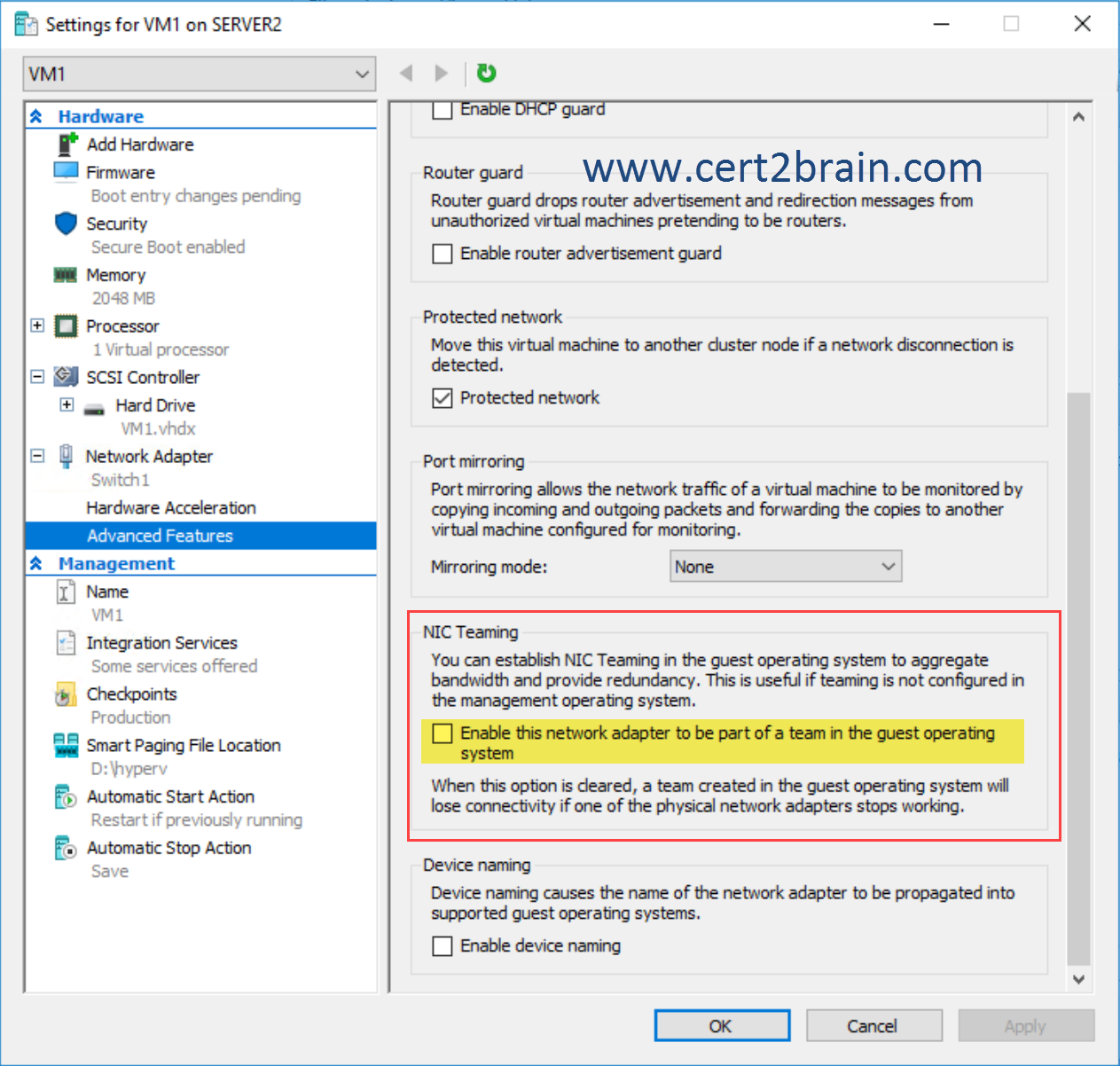
You configure NIC Teaming on VM1 as shown in the following exhibit.
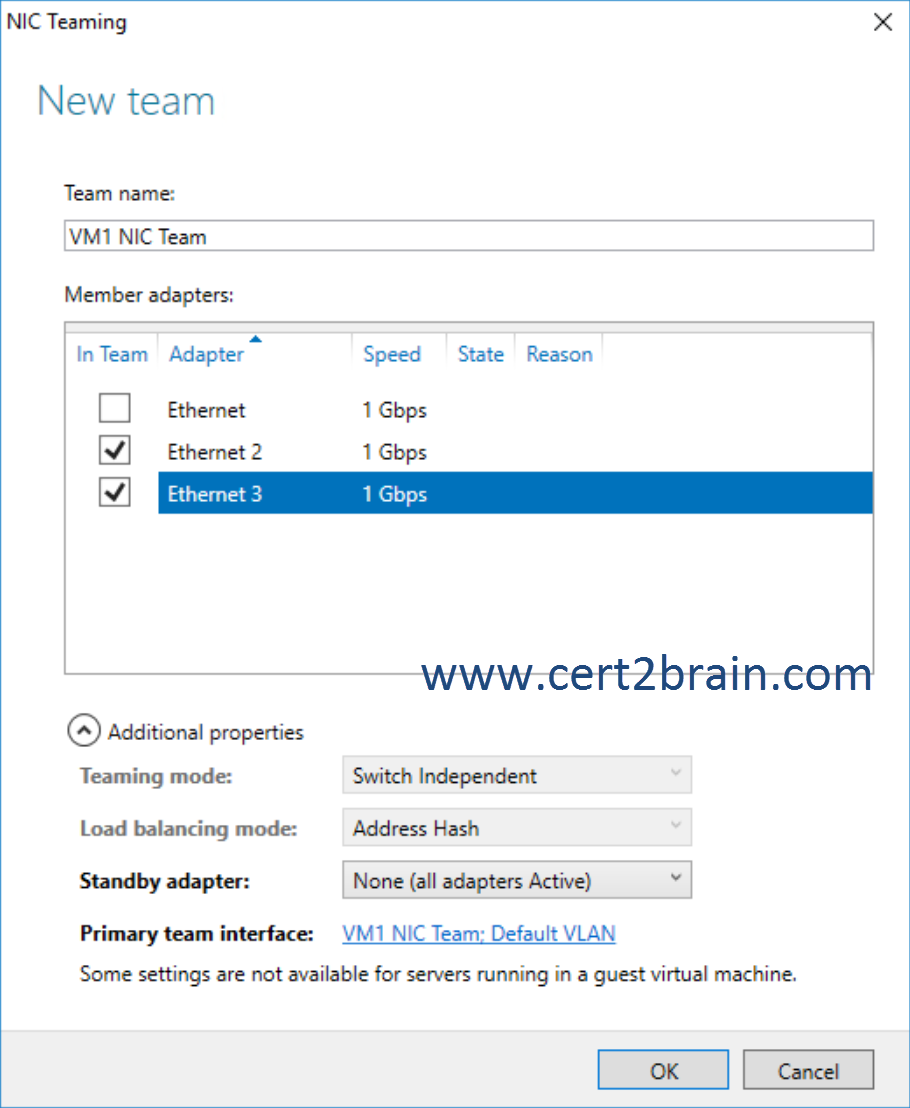
You need to ensure that vm1 will retain access to the network if a physical network adapter card fails on Server1.
What should you do?| A | From the properties of the NIC team on VM1, change the load balancing of the NIC team. |
| B | From Hyper-V Manager on Server1, modify the settings of VM1. |
| C | From Windows PowerShell on Server1, run the Set-VmNetworkAdapterFailoverConfiguration cmdlet. |
| D | From the properties of the NIC team on VM1, add the adapter named Ethernet to the NIC team. |
Correct answer: BExplanation:
The physical switch, Hyper-V Virtual Switch, local area network (LAN), and NIC Teaming requirements for creating a NIC Team in a VM are:
-
The computer running Hyper-V must have two or more network adapters.
-
If connecting the network adapters to multiple physical switches, the physical switches must be on the same Layer 2 subnet.
-
You must use Hyper-V Manager or Windows PowerShell to create two external Hyper-V Virtual Switches, each connected to a different physical network adapter.
-
The VM must connect to both external virtual switches you create.
-
NIC Teaming, in Windows Server 2016, supports teams with two members in VMs. You can create larger teams, but there is no support.
-
If you are configuring a NIC Team in a VM, you must select a Teaming mode of Switch Independent and a Load balancing mode of Address Hash.
We must enable the Enable this network adapter to be part of a team in the guest operating system option to prevent loss of connectivity if one physical network adapter on the host fails.
Reference: Create a new NIC Team on a host computer or VM
Question: 292
Measured Skill: Implement Active Directory Certificate Services (AD CS) (10–15%)
Your network contains an Active Directory domain. The domain contains a server named Server1 that runs Windows Server 2016. Server1 runs a service named Service1 in the security context of the Network Service account.
The domain contains an enterprise certification authority (CA).
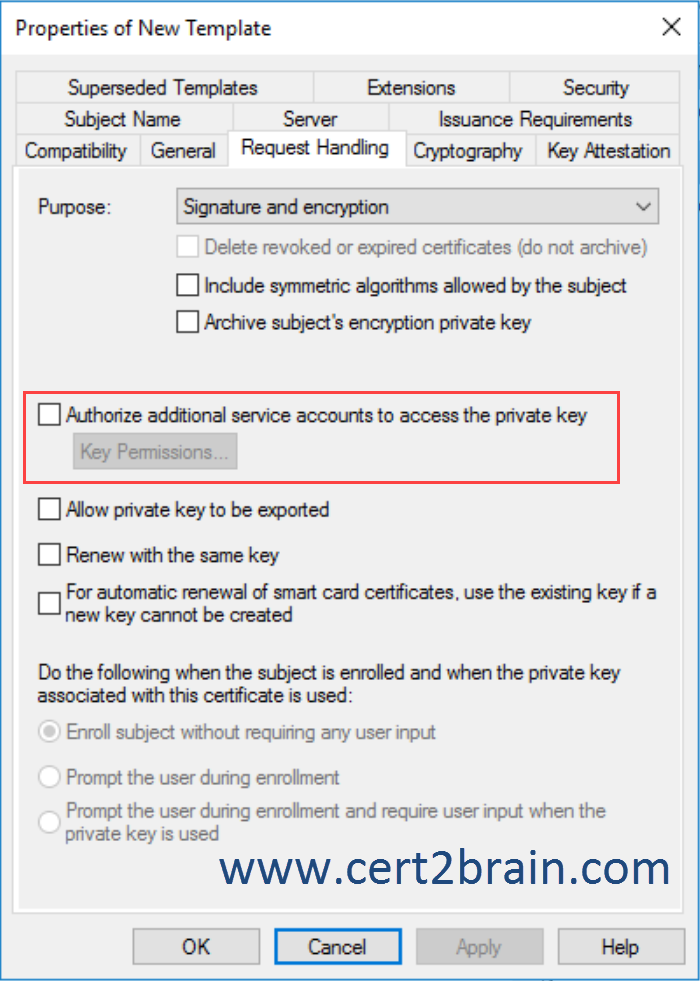
You plan to create a certificate template that will be used to issue certificates for Service1. Server1 will enroll for the certificates on behalf of Service1.
Which template settings you must configure to allow Service1 to access the private keys of the certificates installed on Server1?| A | Extensions |
| B | Issuance Requirements |
| C | Request Handling |
| D | Security |
Correct answer: CExplanation:
On the Request Handling tab in the properties of the duplicated template, we can grant the service account access to the private key of the certificates that are issued based on the template.
 Question: 293
Question: 293
Measured Skill: Implement identity federation and access solutions (15–20%)
Your network contains an Active Directory domain. The domain contains an Active Directory Rights Management Services (AD RMS) cluster.
All client computers run Windows 10 Enterprise.
You need to control from which versions of Windows users can access rights-protected content.
What should you create?| A | A security policy |
| B | A trust policy |
| C | An exclusion policy |
| D | Rights Policy Template |
Correct answer: CExplanation:
You can implement exclusion policies to deny certain entities the ability to acquire certificate and license requests.
There are three ways to exclude these entities:
- by user
- by application
- by lockbox version
The Lockbox property retrieves the minimum lockbox version that must be installed before an end-user license, certificate, or client licensor certificate (CLC) can be granted. The lockbox version depends on the Windows version.
Question: 294
Measured Skill: Manage and maintain AD DS (15–20%)
Your network contains an Active Directory domain named contso.com. Each department at your company has an organizational unit (OU) in Active Directory and a global security group that contains the users in that department.
You need to implement the following security requirements:
- Users in the research department must use complex passwords that are at least 14 characters.
- Users in the finance department must use complex passwords that are at least 10 characters.
- All other users must use an eight-character, non-complex password.
What should you do?| A | From the Default Domain Controller Policy. Modify the Password Policy settings. Create Password settings objects (PSOs) for finance and research. |
| B | From the Default Domain Policy, modify the password policy settings. Create password Settings objects (PSOs) for finance and research. |
| C | Create group Policy objects (GPOs) linked to the finance and research OUs. Modify the Password Policy settings in the Default Domain Policy, the finance GPO and the research GPO. |
| D | Create Group Policy objects (GPOs) linked to the finance and research OUs. Modify the Password Policy settings in the finance GPO and the research GPO. |
Correct answer: BExplanation:
Since Windows Server 2008 you can use fine-grained password policies by implementing Password setting objects (PSOs) to specify multiple password policies in a single domain and apply different restrictions for password and account lockout policies to different sets of users in a domain.
For example, you can apply stricter settings to privileged accounts and less strict settings to the accounts of other users. In other cases, you might want to apply a special password policy for accounts whose passwords are synchronized with other data sources.
Fine-grained password policies apply only to global security groups and user objects. (inetOrgPerson objects if they are used instead of user objects). Fine-grained password policy cannot be applied to an organizational unit (OU) directly.
Other considerations are:
- Only members of the Domain Admins group can set fine-grained password policies. but this can be delegated.
- The domain functional level must be Windows Server 2008.
- Managing the policies is done through Active Directory Administrative Center and/or Windows PowerShell by creating password setting objects (PSO).
Password setting objects (PSO) are not applied on local users that exists on member servers.
In order to configure password settings for local users, we can use the local computer policy (not user policy) or a domain policy that is linked to the organizational unit that contains the computer account of the corresponding domain computer.
Reference: Step-by-Step: Enabling and Using Fine-Grained Password Policies in AD