Microsoft - SC-100: Microsoft Cybersecurity Architect
Sample Questions
Question: 356
Measured Skill: Design security solutions for applications and data (20–25%)
You have 500 on-premises Windows devices that are joined to a Microsoft Entra tenant named Tenant1 and enrolled in Microsoft Intune.
You have an Azure subscription named Sub1 that is linked to Tenant1.
You have a partner company that has an Azure subscription named Sub2. Sub2 contains a virtual network named VNet2 and a storage account named storage1. storage1 is secured by using an Azure Private Link endpoint on VNet2.
You need to recommend a solution to ensures that all the users at your company can access storage1. The solution must meet the following requirements:
- The users must sign in from a compliant device before accessing storage1.
- Access must NOT expose or provide connectivity to any other resources in Sub2.
What should you include in the recommendation, and what should you recommend creating in Tenant1?
(To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.)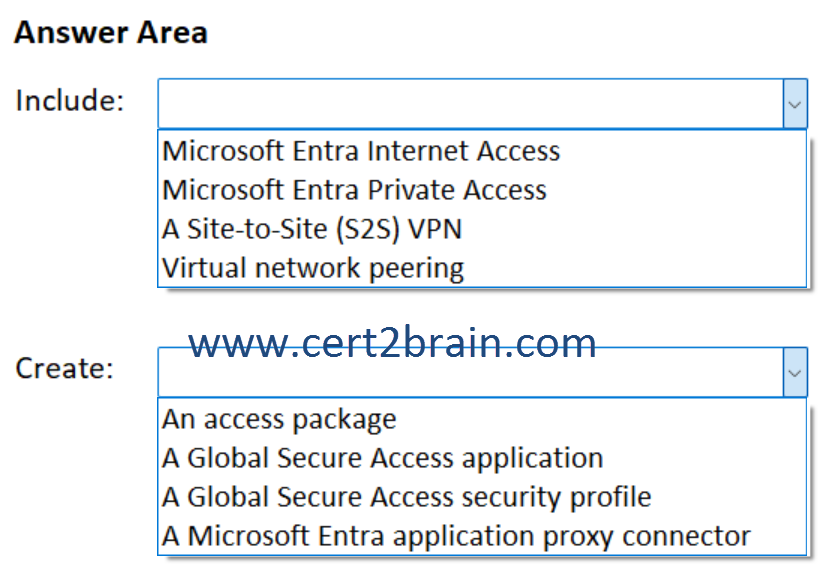
| A | Include: Microsoft Entra Internet Access
Create: A Global Secure Access security profile |
| B | Include: Microsoft Entra Private Access
Create: An access package |
| C | Include: Microsoft Entra Private Access
Create: A Global Secure Access application |
| D | Include: A Site-to-Site (S2S) VPN
Create: A Microsoft Entra application proxy connector |
| E | Include: A Site-to-Site (S2S) VPN
Create: An access package |
| F | Include: Virtual network peering
Create: A Microsoft Entra application proxy connector |
Correct answer: CExplanation:
Microsoft Entra Private Access unlocks the ability to specify the fully qualified domain names (FQDNs) and IP addresses that you consider private or internal, so you can manage how your organization accesses them. With Private Access, you can modernize how your organization's users access private apps and resources. Remote workers don't need to use a VPN to access these resources if they have the Global Secure Access Client installed. The client quietly and seamlessly connects them to the resources they need.
Microsoft Entra Private Access provides per-app access to private resources, works with Azure Private Link internal/private endpoints, and integrates with Conditional Access to enforce the compliant device requirement.
A Global Secure Access application defines the specific private resource users are allowed to connect to.
Reference: Learn about Microsoft Entra Private Access
Question: 357
Measured Skill: Design security operations, identity, and compliance capabilities (30–35%)
Your company has offices in 10 countries.
You have a Microsoft 365 subscription that contains 1,000 users. Each user is assigned a Microsoft 365 E5 license.
You plan to deploy a compliance assessment solution. The solution must meet the following requirements:
- Ensure that compliance is assessed based on the regulations of the country of each office.
- Provide improvement action guidance to ensure compliance of the subscription.
You need to recommend the service that should be used to perform the assessments, and identify additional costs that will be incurred.
What should you recommend and what should you identify?
(To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.)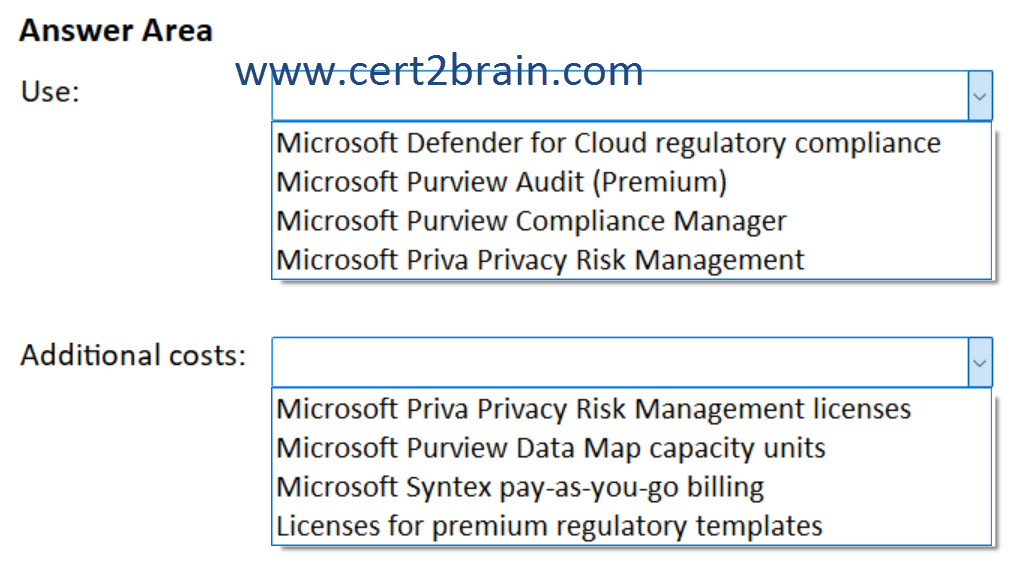
| A | Use: Microsoft Defender for Cloud regulatory compliance
Additional costs: Microsoft Purview Data Map capacity units |
| B | Use: Microsoft Defender for Cloud regulatory compliance
Additional costs: Licenses for premium regulatory templates |
| C | Use: Microsoft Purview Audit (Premium)
Additional costs: Microsoft Priva Privacy Risk Management licenses |
| D | Use: Microsoft Purview Compliance Manager
Additional costs: Licenses for premium regulatory templates |
| E | Use: Microsoft Purview Compliance Manager
Additional costs: Microsoft Priva Privacy Risk Management licenses |
| F | Use: Microsoft Priva Privacy Risk Management
Additional costs: Microsoft Syntex pay-as-you-go billing |
Correct answer: DExplanation:
Compliance Manager assessments help your organization evaluate its compliance with industry and regional regulations. Setting up the most relevant assessments for your organization can help you implement policies and operational procedures to limit your compliance risk. Ready-to-use regulatory templates for over 360 regulations contain the necessary controls and improvement actions for completing the assessment.
Compliance Manager uses regulatory templates to perform assessments. Many country/industry regulations are classified as "premium templates" and require additional licensing.
Improvement actions in Compliance Manager help centralize your compliance activities. Each improvement action recommends an action to take, with detailed guidance intended to help you align with data protection regulations and standards. Improvement actions can be assigned to users in your organization to perform implementation and testing work. You can also store evidence, add notes, and record status updates within the action. Many improvement actions come with automatic testing and monitoring.
References:
Build and manage assessments in Compliance Manager
Working with improvement actions in Compliance Manager
Regulation availability and licensing
Question: 358
Measured Skill: Design security operations, identity, and compliance capabilities (30–35%)
You have a Microsoft 365 subscription that contains 500 users. Each user is assigned a Microsoft 365 E5 license and uses a Windows device.
Microsoft Purview data loss prevention (DLP) policies are applied to Microsoft Exchange Online email and SharePoint Online sites.
You plan to monitor the usage of third-party generative AI apps by using Microsoft Purview Data Security Posture Management for AI (DSPM for AI).
What should you do first?| A | Enable Microsoft Purview insider risk management for all the users. |
| B | Onboard all endpoint devices to Microsoft Purview. |
| C | Configure Microsoft Purview data connectors for the generative AI apps. |
| D | License all the users for Microsoft 365 Copilot. |
Correct answer: BExplanation:
To use Data Security Posture Management for AI from the Microsoft Purview portal, you must have the following prerequisites:
You have the right permissions.
Required for monitoring interactions with Copilot and agents:
Microsoft Purview auditing is enabled for your organization. Although this is the default, you might want to check the instructions for Turn auditing on or off.
For Microsoft 365 Copilot and agents, users are assigned a license for Microsoft 365 Copilot.
For Copilot in Fabric and Security Copilot:
- The enterprise version of Microsoft Purview data governance, to support the required APIs.
- A collection policy, such as the one created from the recommendation or remediation action Secure interactions for Microsoft Copilot experiences.
Required for monitoring interactions and applying DLP policies to other AI apps in Edge:
- An Edge configuration policy is required to activate the Microsoft Purview integration in Edge. For configuration information, see Activate your DLP policy in Microsoft Edge.
Required for monitoring interactions with third-party generative AI sites:
Devices are onboarded to Microsoft Purview, required for:
- Gaining visibility into sensitive information that's shared with third-party generative AI sites. For example, a user pastes credit card numbers into ChatGPT.
- Applying endpoint DLP policies to warn or block users from sharing sensitive information with third-party generative AI sites. For example, a user identified as elevated risk in Adaptive Protection is blocked with the option to override when they paste credit card numbers into ChatGPT.
The Microsoft Purview browser extension is deployed to Windows users and required to discover visits to third-party generative AI sites by using an Insider Risk Management policy. The browser extension is also required for Endpoint DLP policies on Windows when you use Chrome.
For Entra-registered AI apps, they are integrated with the Microsoft Purview SDK to support all the Microsoft Purview capabilities.
For AI apps other than Microsoft 365 Copilot and Microsoft Facilitator, you've set up pay-as-you-go billing for your organization. When this billing model is applicable for specific configurations, you'll see notifications and instructions in the UI.
Reference: Considerations for DSPM for AI to manage data security and compliance protections for AI interactions - (classic)
Question: 359
Measured Skill: Design security solutions for applications and data (20–25%)
You have an Azure subscription that contains an Azure Synapse Analytics workspace named workspace1. workspace1 contains a built-in serverless SQL pool and a dedicated SQL pool named Pool1.
You need to recommend a second layer of data encryption for workspace1.
What should you include in the recommendation for each pool?
(To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.)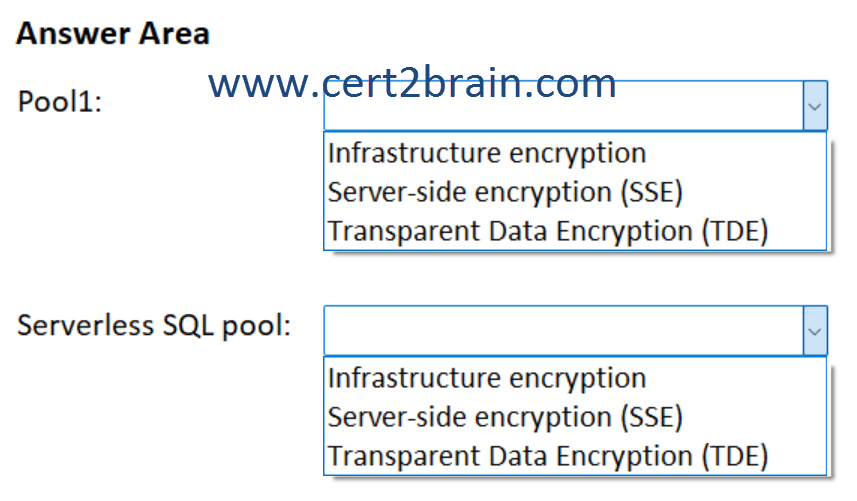
| A | Pool1: Infrastructure encryption
Serverless SQL pool: Server-side encryption (SSE) |
| B | Pool1: Infrastructure encryption
Serverless SQL pool: Transparent Data Encryption (TDE) |
| C | Pool1: Server-side encryption (SSE)
Serverless SQL pool: Infrastructure encryption |
| D | Pool1: Server-side encryption (SSE)
Serverless SQL pool: Transparent Data Encryption (TDE) |
| E | Pool1: Transparent Data Encryption (TDE)
Serverless SQL pool: Infrastructure encryption |
| F | Pool1: Transparent Data Encryption (TDE)
Serverless SQL pool: Server-side encryption (SSE) |
Correct answer: EExplanation:
A complete Encryption-at-Rest solution ensures the data is never persisted in unencrypted form. Double encryption of data at rest mitigates threats with two, separate layers of encryption to protect against compromises of any single layer. Azure Synapse Analytics offers a second layer of encryption for the data in your workspace with a customer-managed key. This key is safeguarded in your Azure Key Vault, which allows you to take ownership of key management and rotation.
The first layer of encryption for Azure services is enabled with platform-managed keys. By default, Azure Disks, and data in Azure Storage accounts are automatically encrypted at rest.
The data in the following Synapse components is encrypted with the customer-managed key configured at the workspace level:
- SQL pools
- Dedicated SQL pools
- Serverless SQL pools
- Data Explorer pools
- Apache Spark pools
- Azure Data Factory integration runtimes, pipelines, datasets.
By default, Azure Storage automatically encrypts all data using 256-bit Advanced Encryption Standard encryption (AES 256). It's one of the strongest block ciphers available and is FIPS 140-2 compliant. The platform manages the encryption key, and it forms the first layer of data encryption. This encryption applies to both user and system databases, including the master database.
Enabling Transparent Data Encryption (TDE) can add a second layer of data encryption for dedicated SQL pools. It performs real-time I/O encryption and decryption of database files, transaction logs files, and backups at rest without requiring any changes to the application. By default, it uses AES 256.
By default, TDE protects the database encryption key (DEK) with a built-in server certificate (service managed). There's an option to bring your own key (BYOK) that can be securely stored in Azure Key Vault.
Azure Synapse SQL serverless pool and Apache Spark pool are analytic engines that work directly on Azure Data Lake Gen2 (ALDS Gen2) or Azure Blob Storage. These analytic runtimes don't have any permanent storage and rely on Azure Storage encryption technologies for data protection. By default, Azure Storage encrypts all data using server-side encryption (SSE). It's enabled for all storage types (including ADLS Gen2) and cannot be disabled. SSE encrypts and decrypts data transparently using AES 256.
There are two SSE encryption options:
Microsoft-managed keys: Microsoft manages every aspect of the encryption key, including key storage, ownership, and rotations. It's entirely transparent to customers.
Customer-managed keys: In this case, the symmetric key used to encrypt data in Azure Storage is encrypted using a customer-provided key. It supports RSA and RSA-HSM (Hardware Security Modules) keys of sizes 2048, 3072, and 4096. Keys can be securely stored in Azure Key Vault or Azure Key Vault Managed HSM. It provides fine grain access control of the key and its management, including storage, backup, and rotations. For more information, see Customer-managed keys for Azure Storage encryption.
While SSE forms the first layer of encryption, cautious customers can double encrypt by enabling a second layer of 256-bit AES encryption at the Azure Storage infrastructure layer. Known as infrastructure encryption, it uses a platform-managed key together with a separate key from SSE. So, data in the storage account is encrypted twice; once at the service level and once at the infrastructure level with two different encryption algorithms and different keys.
References:
Encryption for Azure Synapse Analytics workspaces
Azure Synapse Analytics security white paper: Data protection
Question: 360
Measured Skill: Design security operations, identity, and compliance capabilities (30–35%)
You have a Microsoft Entra tenant that contains two users named User1 and User2.
A recent audit reveals that User1 has a permanent assignment to the User Administrator role, even though the user account belongs to a former contractor.
The security team at your company has the following requirements:
- Ensure that all privileged role assignments are periodically validated.
- Use Privileged Identity Management (PIM) to automate and enforce the validation process.
You need to ensure that User2 can meet the security requirements. The solution must follow the principle of least privilege.
Which role should you assign to User2, and what should User2 use?
(To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.)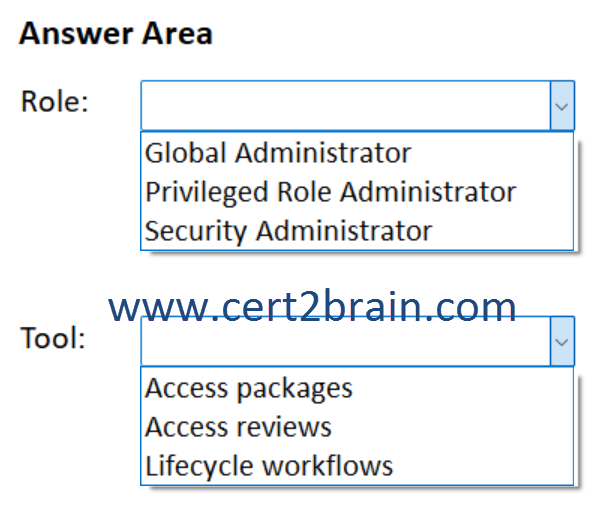
| A | Role: Global Administrator
Tool: Access reviews |
| B | Role: Global Administrator
Tool: Access packages |
| C | Role: Privileged Role Administrator
Tool: Access reviews |
| D | Role: Privileged Role Administrator
Tool: Lifecycle workflows |
| E | Role: Security Administrator
Tool: Access packages |
| F | Role: Security Administrator
Tool: Lifecycle workflows |
Correct answer: CExplanation:
The need for access to privileged Azure resource and Microsoft Entra roles by your users changes over time. To reduce the risk associated with stale role assignments, you should regularly review access. You can use Microsoft Entra Privileged Identity Management (PIM) to create access reviews for privileged access to Azure resource and Microsoft Entra roles. You can also configure recurring access reviews that occur automatically.
To create access reviews for Azure resources, you must be assigned to the Owner or the User Access Administrator role for the Azure resources. To create access reviews for Microsoft Entra roles, you must be assigned at least the Privileged Role Administrator role.
Reference: Create an access review of Azure resource and Microsoft Entra roles in PIM