Microsoft - SC-300: Microsoft Identity and Access Administrator
Sample Questions
Question: 427
Measured Skill: Implement authentication and access management (25–30%)
You have on-premises Linux devices.
You have a Microsoft 365 E5 subscription.
You plan to configure Global Secure Access Internet Access.
You need to ensure that the devices can connect to Global Secure Access.
What should you do?| A | Configure the Adaptive Access settings. |
| B | Install the Azure Connected Machine agent on the devices. |
| C | Create a remote network. |
| D | Deploy a private network connector. |
Correct answer: CExplanation:
Microsoft Entra Internet Access and Microsoft Entra Private Access comprise Microsoft's Security Service Edge (SSE) solution. Global Secure Access is the unifying term used for both Microsoft Entra Internet Access and Microsoft Entra Private Access. Global Secure Access is the unified location in the Microsoft Entra admin center. Global Secure Access is built upon the core principles of Zero Trust to use least privilege, verify explicitly, and assume breach.
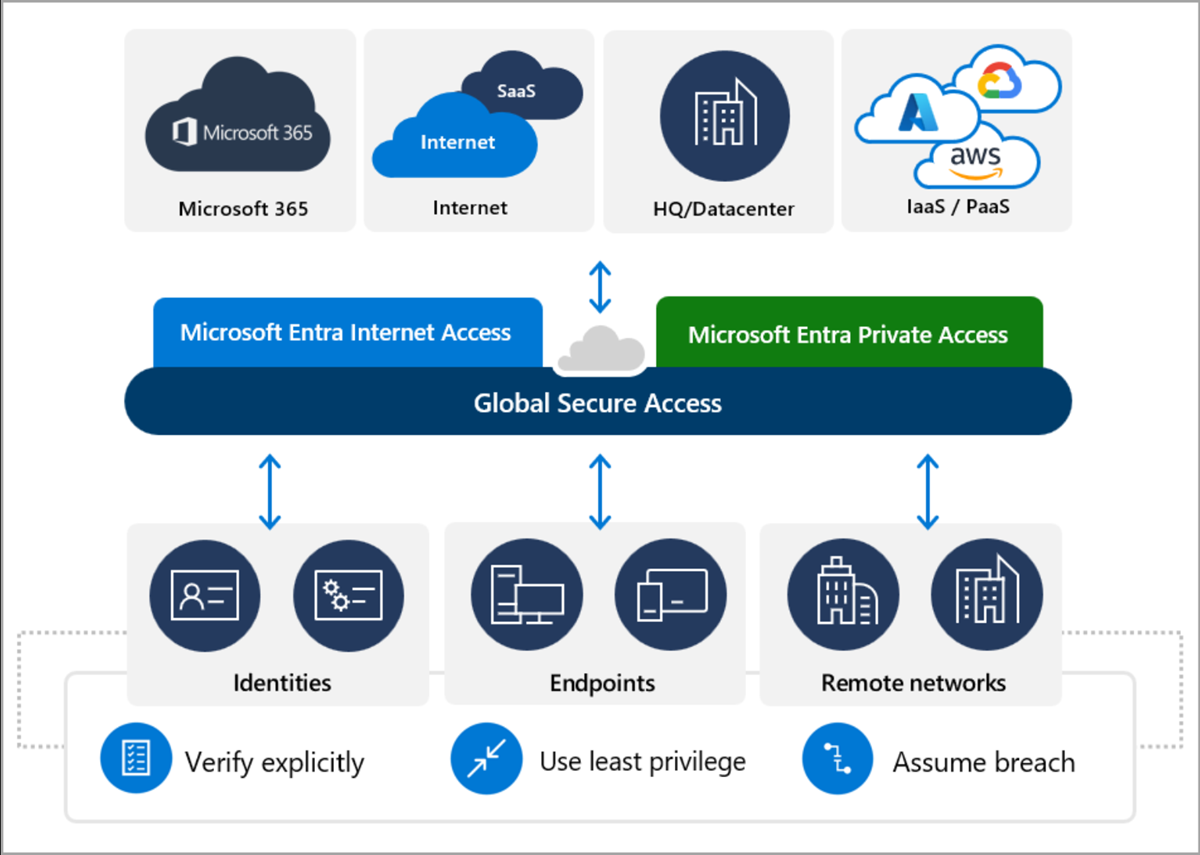
Global Secure Access supports two connectivity options: installing a client on end-user device and configuring a remote network, for example a branch location with a physical router. The Global Secure Access client is available for Windows, macOS, Android, and iOS, but not for Linux. Remote network connectivity supports any operating system.
References:
What is Global Secure Access?
Understand remote network connectivity
Known limitations for Global Secure Access
Question: 428
Measured Skill: Implement authentication and access management (25–30%)
You have a Microsoft Entra tenant that contains 1,000 users. The users are assigned Microsoft Entra Suite licenses.
You perform the following actions:
- Deploy Global Secure Access.
- Create a Global Secure Access security profile named Profile1.
- Create the following Conditional Access policy:
- Name: CAPolicy1
- Target resources: All internet resources with Global Secure Access
- Session: Use Global Secure Access security profile: Profile1
To which Global Secure Access traffic forwarding profiles is CAPolicy1 linked, and to which profile does Profile1 apply?
(To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.)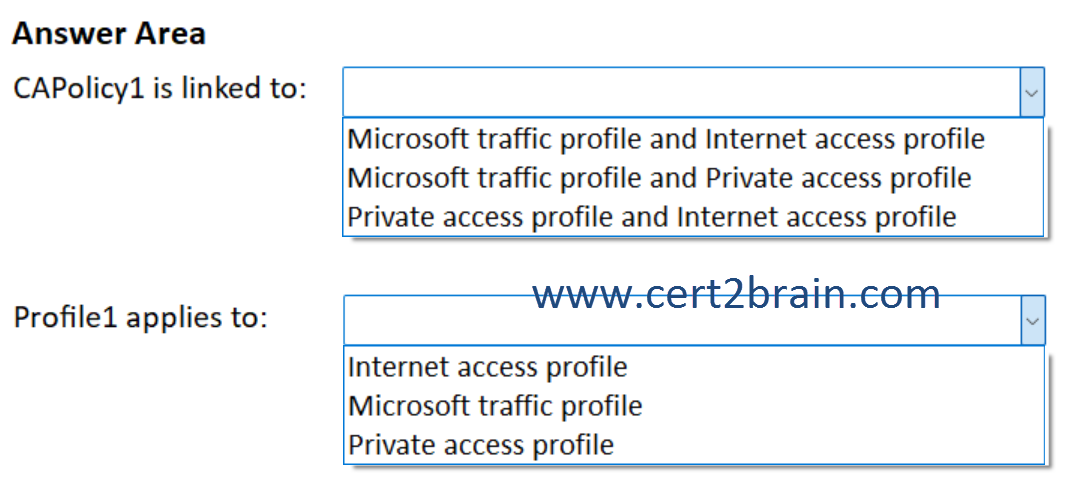
| A | CAPolicy1 is linked to: Microsoft traffic profile and Internet access profile
Profile1 applies to: Private access profile |
| B | CAPolicy1 is linked to: Microsoft traffic profile and Internet access profile
Profile1 applies to: Internet access profile |
| C | CAPolicy1 is linked to: Microsoft traffic profile and Private access profile
Profile1 applies to: Microsoft traffic profile |
| D | CAPolicy1 is linked to: Microsoft traffic profile and Private access profile
Profile1 applies to: Internet access profile |
| E | CAPolicy1 is linked to: Private access profile and Internet access profile
Profile1 applies to: Private access profile |
| F | CAPolicy1 is linked to: Private access profile and Internet access profile
Profile1 applies to: Microsoft traffic profile |
Correct answer: BExplanation:
In Global Secure Access (GSA), traffic is split into three forwarding profiles:
Microsoft traffic profile - Microsoft 365 and other Microsoft cloud services
Internet access profile - General internet (non-Microsoft SaaS, public websites)
Private access profile - Private apps published via GSA (replaces VPN scenarios)
CAPolicy1 targets All internet resources with Global Secure Access. When you target All internet resources with Global Secure Access, the policy applies to Microsoft traffic and Internet access. It does not apply to Private access, because private access uses enterprise/private applications, not internet resources.
Global Secure Access security profiles are used to inspect and control general internet traffic, not Microsoft-optimized traffic or private app traffic. Even though CAPolicy1 is linked to both forwarding profiles when you target All internet resources with Global Secure Access, the security profile itself is applied to the Internet access profile only.
References:
What is Global Secure Access?
Global Secure Access traffic forwarding profiles
How to configure Global Secure Access web content filtering
Question: 429
Measured Skill: Implement authentication and access management (25–30%)
Your network contains an on-premises Active Directory Domain Services (AD DS) domain. The domain contains 500 Windows 11 devices.
You have a Microsoft 365 subscription that syncs with the domain.
You create a Conditional Access policy named Policy1.
You need to meet the following requirements:
- Apply Policy1 to all the Windows devices.
- Assess the compliance of the Windows devices with Policy1.
What should you do for each requirement?
(To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.)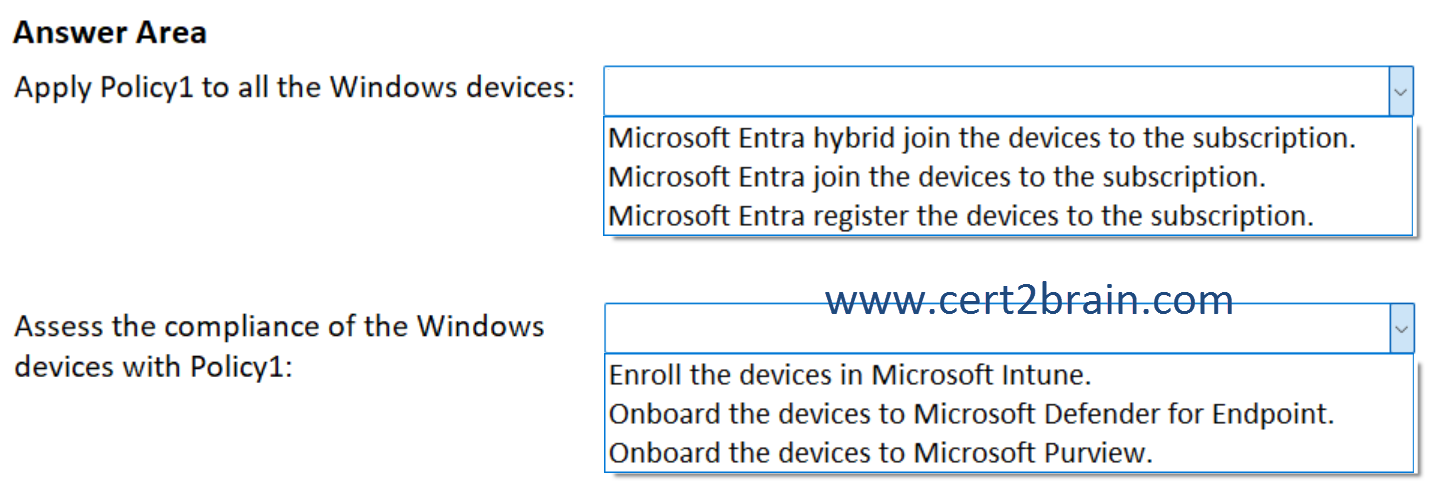
| A | Apply Policy1 to all the Windows devices: Microsoft Entra hybrid join the devices to the subscription.
Assess the compliance of the Windows devices with Policy1: Enroll the devices in Microsoft Intune. |
| B | Apply Policy1 to all the Windows devices: Microsoft Entra hybrid join the devices to the subscription.
Assess the compliance of the Windows devices with Policy1: Onboard the devices to Microsoft Purview. |
| C | Apply Policy1 to all the Windows devices: Microsoft Entra join the devices to the subscription.
Assess the compliance of the Windows devices with Policy1: Onboard the devices to Microsoft Defender for Endpoint. |
| D | Apply Policy1 to all the Windows devices: Microsoft Entra join the devices to the subscription.
Assess the compliance of the Windows devices with Policy1: Onboard the devices to Microsoft Purview. |
| E | Apply Policy1 to all the Windows devices: Microsoft Entra register the devices to the subscription.
Assess the compliance of the Windows devices with Policy1: Enroll the devices in Microsoft Intune. |
| F | Apply Policy1 to all the Windows devices: Microsoft Entra register the devices to the subscription.
Assess the compliance of the Windows devices with Policy1: Onboard the devices to Microsoft Defender for Endpoint. |
Correct answer: AExplanation:
The 500 Windows 11 devices are joined to the on-premises Active Directory Domain Services (AD DS) domain. To ensure, that we can apply an Entra ID Conditional Access policy to the devices, we need to implement Microsoft Entra Connect or Microsoft Entra Cloud Connect and sync computer objects of the devices to Entra ID. Microsoft Entra hybrid joined devices are joined to your on-premises Active Directory and registered with Microsoft Entra ID.
To assess the compliance of the Windows devices, we need to enroll the devices in Microsoft Intune and apply an Intune compliance policy. Microsoft Intune compliance policies are sets of rules and conditions that you use to evaluate the configuration of your managed devices. These policies can help you secure organizational data and resources from devices that don't meet those configuration requirements. Managed devices must satisfy the conditions you set in your policies to be considered compliant by Intune.
References:
Microsoft Entra hybrid joined devices
Use compliance policies to set rules for devices you manage with Intune
Question: 430
Measured Skill: Implement authentication and access management (25–30%)
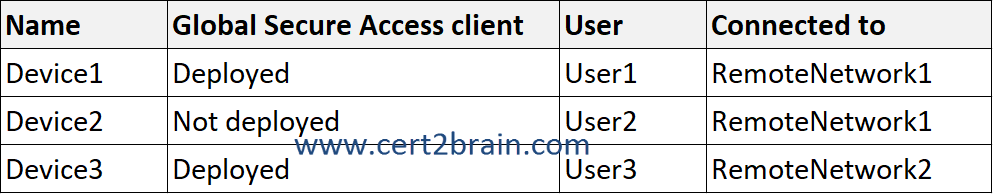
You have a Microsoft Entra tenant that contains two remote networks named RemoteNetwork1 and RemoteNetwork2 and the users shown in the following table.
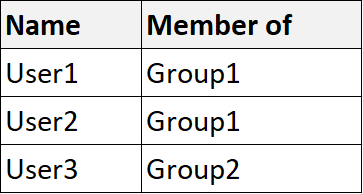
You have the devices shown in the following table.
You have a Conditional Access policy that has the following settings:
- Name: CAPolicy1
- Assignments
- Users: Group1, Group2
- Target resources: All internet resources with Global Secure Access
- Access controls
- Grant: Require multifactor authentication
Enable policy: On
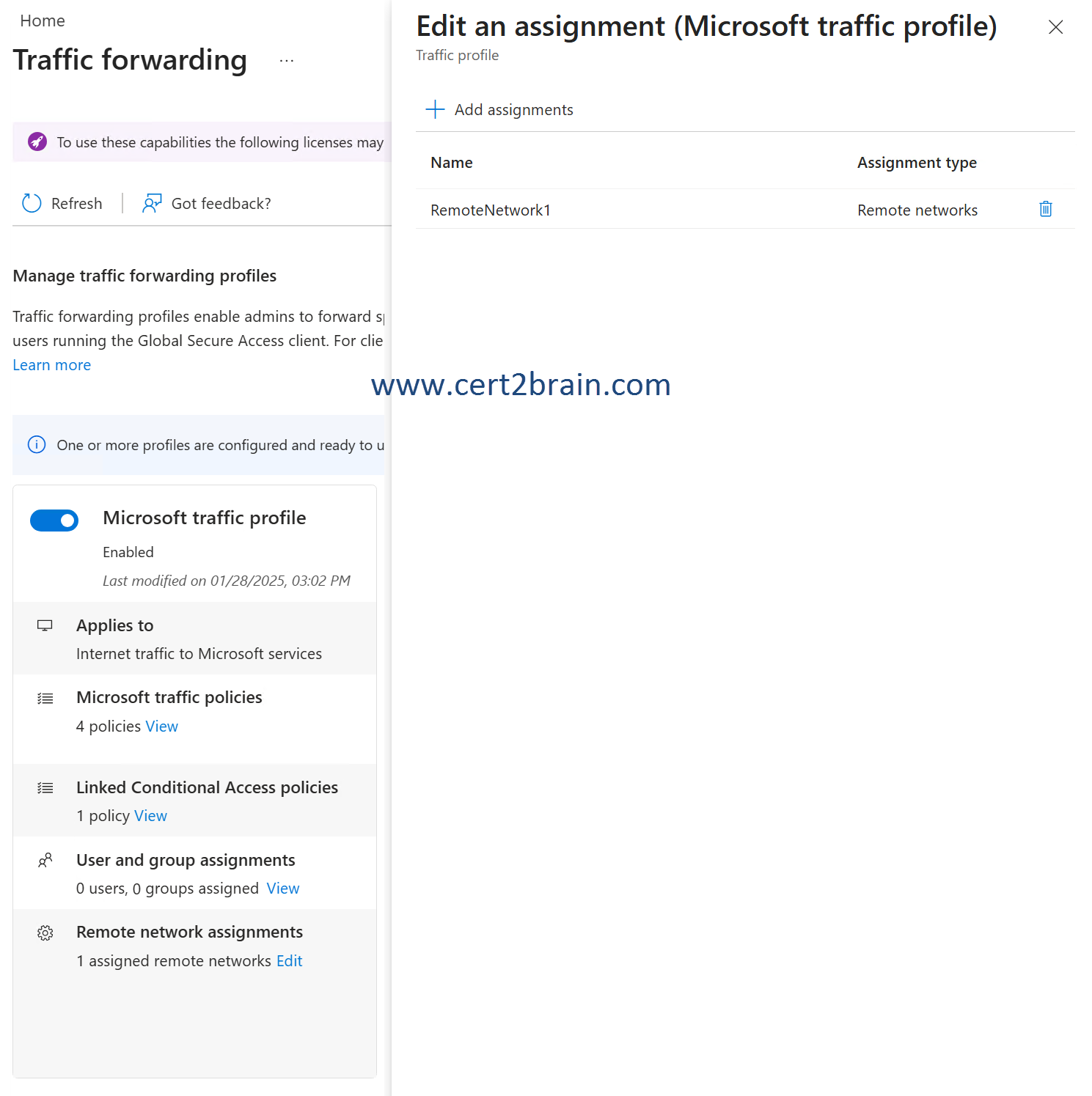
Global Secure Access traffic forwarding is configured as shown in the following exhibit.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
(NOTE: Each correct selection is worth one point.)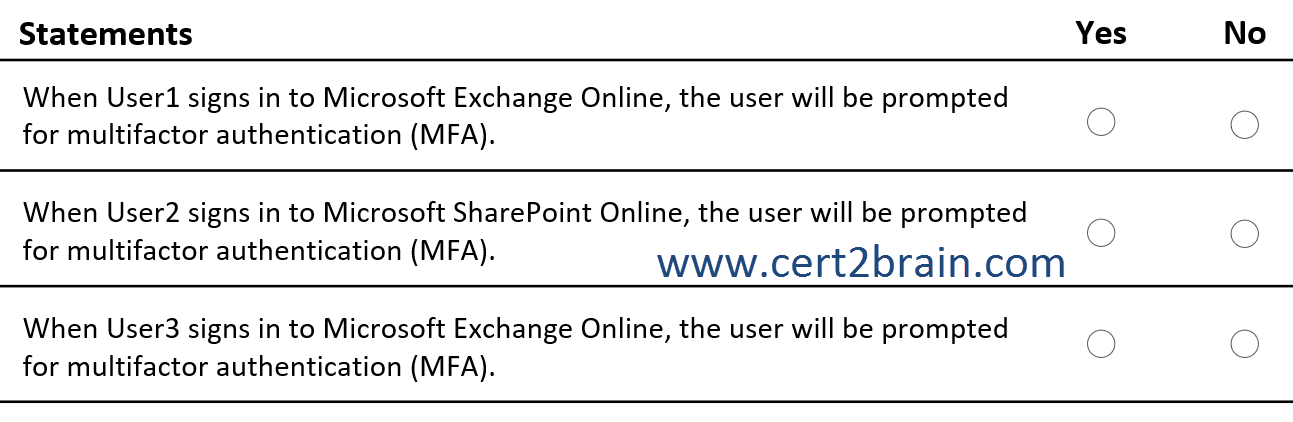
| A | When User1 signs in to Microsoft Exchange Online, the user will be prompted for multifactor authentication (MFA): Yes
When User2 signs in to Microsoft SharePoint Online, the user will be prompted for multifactor authentication (MFA): Yes
When User3 signs in to Microsoft Exchange Online, the user will be prompted for multifactor authentication (MFA): Yes |
| B | When User1 signs in to Microsoft Exchange Online, the user will be prompted for multifactor authentication (MFA): Yes
When User2 signs in to Microsoft SharePoint Online, the user will be prompted for multifactor authentication (MFA): Yes
When User3 signs in to Microsoft Exchange Online, the user will be prompted for multifactor authentication (MFA): No |
| C | When User1 signs in to Microsoft Exchange Online, the user will be prompted for multifactor authentication (MFA): Yes
When User2 signs in to Microsoft SharePoint Online, the user will be prompted for multifactor authentication (MFA): No
When User3 signs in to Microsoft Exchange Online, the user will be prompted for multifactor authentication (MFA): Yes |
| D | When User1 signs in to Microsoft Exchange Online, the user will be prompted for multifactor authentication (MFA): No
When User2 signs in to Microsoft SharePoint Online, the user will be prompted for multifactor authentication (MFA): Yes
When User3 signs in to Microsoft Exchange Online, the user will be prompted for multifactor authentication (MFA): Yes |
| E | When User1 signs in to Microsoft Exchange Online, the user will be prompted for multifactor authentication (MFA): No
When User2 signs in to Microsoft SharePoint Online, the user will be prompted for multifactor authentication (MFA): No
When User3 signs in to Microsoft Exchange Online, the user will be prompted for multifactor authentication (MFA): Yes |
| F | When User1 signs in to Microsoft Exchange Online, the user will be prompted for multifactor authentication (MFA): No
When User2 signs in to Microsoft SharePoint Online, the user will be prompted for multifactor authentication (MFA): No
When User3 signs in to Microsoft Exchange Online, the user will be prompted for multifactor authentication (MFA): No |
Correct answer: BExplanation:
Traffic forwarding profiles enable admins to forward specific traffic to Global Secure Access. We can assign traffic forwarding profiles to users running the Global Secure Access client or to remote networks for clientless devices.
In Global Secure Access (GSA), traffic is split into three forwarding profiles:
Microsoft traffic profile - Microsoft 365 and other Microsoft cloud services
Internet access profile - General internet (non-Microsoft SaaS, public websites)
Private access profile - Private apps published via GSA (replaces VPN scenarios)
CAPolicy1 targets All internet resources with Global Secure Access. When you target All internet resources with Global Secure Access, the policy applies to Microsoft traffic and Internet access. Here, only the Microsoft traffic profile is enabled. So, Global Secure Access will only affect traffic to Microsoft 365 and other Microsoft cloud services.
User1 is connected to RemoteNetwork1 and a member of Group1. When User1 signs in to Microsoft Exchange Online, CAPolicy1 applies and requires multifactor authentication (MFA).
User2 is connected to RemoteNetwork1 and a member of Group1. When User2 signs in to Microsoft SharePoint Online, CAPolicy1 applies and requires multifactor authentication (MFA).
User3 is connected to RemoteNetwork2 and a member of Group2. When User3 signs in to Microsoft Exchange Online, CAPolicy1 does not apply and User3 will not be prompted for multifactor authentication (MFA).
References:
What is Global Secure Access?
Global Secure Access traffic forwarding profiles
How to create a remote network with Global Secure Access
Question: 431
Measured Skill: Implement authentication and access management (25–30%)
You have a Microsoft Entra tenant.
You have 500 devices that run either Windows 11, macOS, iOS, or Android and are enrolled in Microsoft Intune.
You plan to deploy the Global Secure Access client.
From the Microsoft Entra admin center, you download the Global Secure Access client for each operating system.
You need to deploy the client to the macOS devices by using Intune.
Which file extension should you use when uploading the client to Intune?| A | .ipa |
| B | .apk |
| C | .intunewin |
| D | .pkg |
Correct answer: DExplanation:
The Global Secure Access client, an essential component of Global Secure Access, helps organizations manage and secure network traffic on end-user devices. The client's main role is to route traffic that needs to be secured by Global Secure Access to the cloud service. All other traffic goes directly to the network. The Forwarding Profiles, configured in the portal, determine which traffic the Global Secure Access client routes to the cloud service.
You install the client on a device, such as computer or phone, and then use Global Secure Access settings in the Microsoft Entra admin center to secure the device. Clients are currently available for Windows, Android, macOS, and iOS.
For macOS app deployment through Intune, you upload the installer package format used by macOS, which is a .pkg file (GlobalSecureAccessClient.pkg).
References:
Global Secure Access client overview
Install the Global Secure Access client for macOS